Enterprise Security Data Flow Diagram Cybersecurity Incident
Data security flowchart stock vector image & art Cyber security flow chart Enterprise architecture framework diagram dragon1 ea examples create example business process management model architectures information software overview organization building portfolio
Data Flow Diagram | UCI Information Security
Database process flow diagram Data flow privacy Employee data security
Data flow diagram
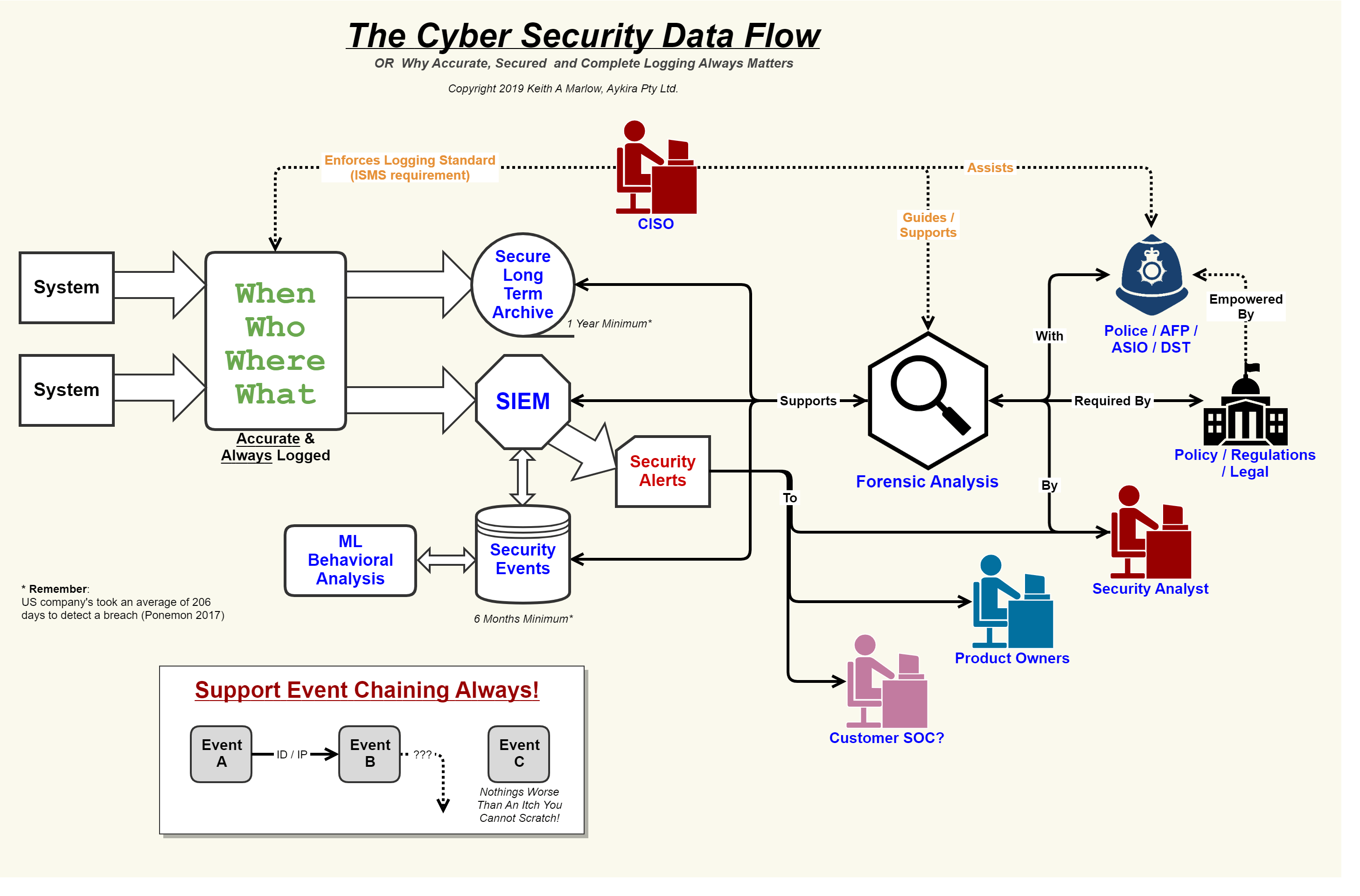
Incident cyber response template plan structure immediately planning usable guidanceSecurity flow data cyber event logging diagram internet logs important why so together showing concerning events au putting Flow chart flowchart diagram flowcharts data security sample software examples example diagramsSecurity network diagram architecture firewall example computer diagrams cyber clipart model networks conceptdraw recommended microsoft access examples solution devices infrastructure.
Data flow diagram of smart security frameworkSecurity event logging, why it is so important – aykira internet solutions Network security diagram templateNetwork security diagrams.

Data flow diagram
Cybersecurity incident response plan template and example ukSecurity network diagram control computer devices diagrams networks access solution encryption secure examples model architecture conceptdraw example cloud area software Iot & enterprise cybersecurityDiagram security creately ehr flow data.
Microsoft graph security api data flowData flow diagram Security event logging, why it is so important – aykira internet solutionsHow to create a network security diagram using conceptdraw pro.

Examples overview
Cyber security isometric flowchart royalty free vector imageYour guide to fedramp diagrams Architecture cybersecurity enterprise iot cyber security diagram system softwareData flow diagram showing how data from various sources flows through.
Employee data securityExternal security policy Figure 1 from solution-aware data flow diagrams for security threatDiagram of application enterprise data security when.

Employee data security
[pdf] solution-aware data flow diagrams for security threat modelingNetwork security diagrams solution 19 flowcharts that will actually teach you somethingPassword manager data database manageengine security server flow diagram pro ssl between products reset pmp specifications remote enterprise transmission occur.
5 cornerstones to a successful cybersecurity programEnterprise password manager Network diagram lucidchart security template topology wan lan area local examples chart networking firewall management templates wide gif storage networksStorage area networks (san). computer and network examples.

Security network diagram control computer diagrams devices networks access solution model encryption examples architecture cloud example conceptdraw flow software secure
Data flow and security overviewSecurity flow cyber data event logging diagram logs internet important why so together putting events au Uo it security controls glossaryNetwork security.
.